Bitvise Ssh Server Generate Key
Host Key Authentication with SFTP. Host Key Authentication with SFTP. Titan FTP Server can use Secure File Transfer Protocol (SFTP), a Host Key Authentication method which. Adds Secure Shell (SSH) protection to your data transfers. Most encryption methods for information transfer involve Public Key Infrastructure (PKI), which is the. Jan 11, 2007 Generating a SSH key public/private key pair Before we can even authenticate to the remote machine using key based authentication, we need to create a public/private key pair. To do so, simply trigger: $ ssh-keygen Generating public/private rsa key pair.
If your SSH client supports it, you can use public key authentication to log into Bitvise SSH Server. On Windows, we recommend Bitvise SSH Client, which has strong support for public key authentication, as well as password authentication, and Kerberos single sign-on in domain environments.
If you are new to public key authentication, we first suggest reading Public keys in SSH.
- Chocolatey is software management automation for Windows that wraps installers, executables, zips, and scripts into compiled packages. Chocolatey integrates w/SCCM, Puppet, Chef, etc. Chocolatey is trusted by businesses to manage software deployments.
- Mar 23, 2019 Bitvise SSH Server (previously WinSSHD) provides secure remote login capabilities. Security is our SSH server's key feature: in contrast with Telnet and FTP servers, Bitvise SSH Server encrypts data during transmission. Thus, no one can sniff your password or see what files you are transferring when you access your computer over SSH.
To set up public key authentication, you first need to generate a keypair on the client, or select one or more existing keypairs for use with client authentication. The procedure for generating the keypair depends on the client software being used:
- If you are using Bitvise SSH Client, click the link titled Client key manager in the Login tab. You can generate, edit, import and export keypairs in the dialog box that pops up.
- If you are using a different client, you need to follow its process for generating keypairs. For example, in OpenSSH, keypairs are generated using the ssh-keygen utility. Make sure to generate an SSH2 keypair (not SSH1). Use either the ECDSA, RSA, or DSA (DSS) algorithms. We recommend either ECDSA, or RSA with a size of 2048 bits or higher.
Once the keypair has been generated, you need to import the public key (not the whole keypair!) into the SSH Server.
Recent Bitvise SSH Server and SSH Client versions support the SSH Public Key Subsystem. To import a public key into the SSH Server this way:
- Use the SSH Client to connect to the SSH Server using the account for which you want to configure the public key.
- Once connected, open Client key manager. Right-click on the keypair, and select Upload to server.
- You should now be able to authenticate using this keypair.
You can also use this feature to manage keys in the SSH Server from the command line, using the spksc client included with Bitvise SSH Client.
With most clients, you can export the public key into a file, transfer the file to the SSH Server, and import it into SSH Server settings. In this case:
- Export the public key in either the standard SSH2 public key format, or in the OpenSSH format. If you are using OpenSSH, the public key file can be exported from an existing keypair using the ssh-keygen utility (consult 'man ssh-keygen').
- Once your public key file has been exported, transfer it to the machine where Bitvise SSH Server is installed, or a machine from which you manage the SSH Server remotely using Bitvise SSH Client.
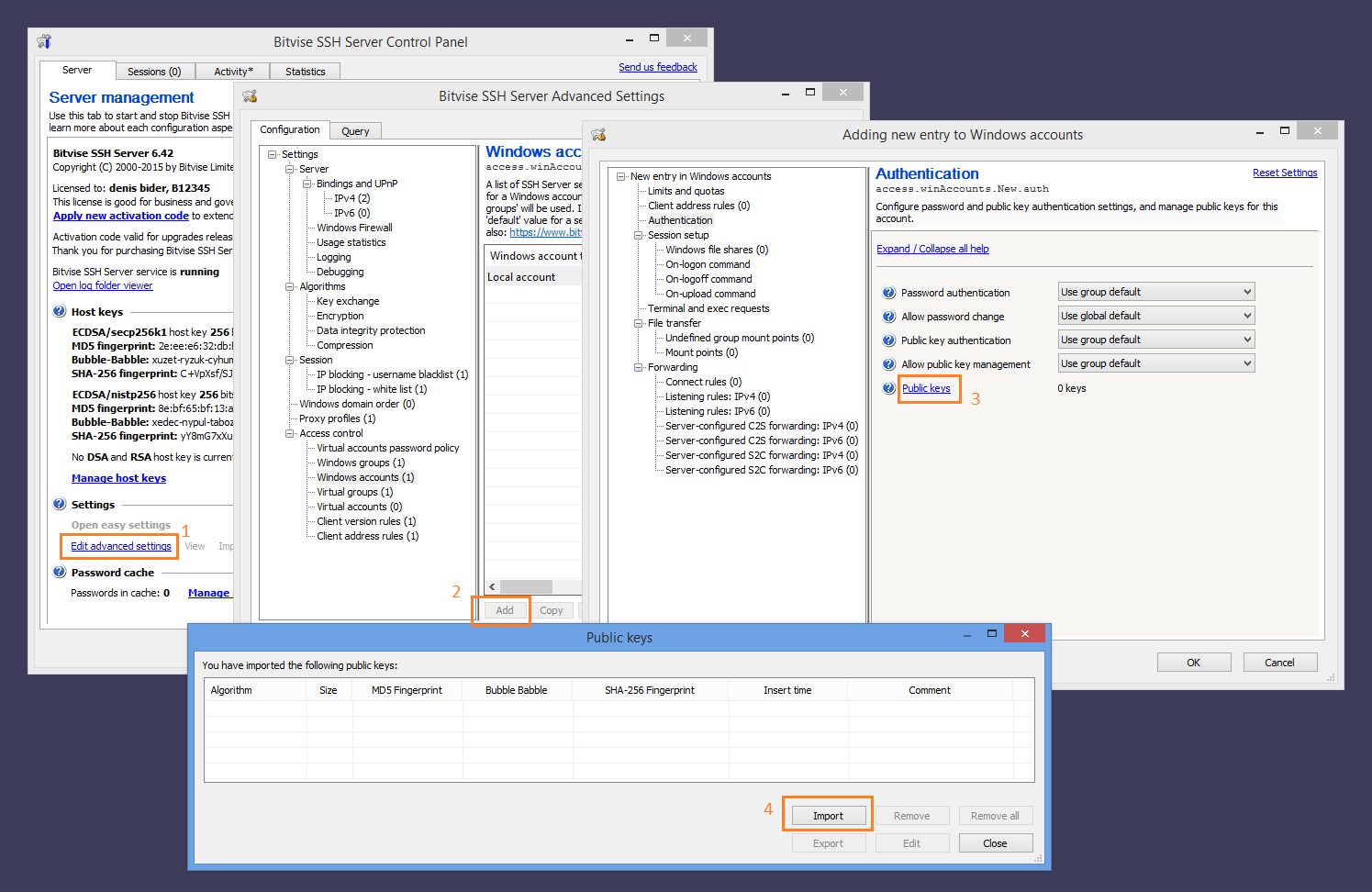
- Use either Easy SSH Server settings (screenshot) or Advanced settings (screenshot) to import the public key into the SSH user's account settings entry.
Common mistakes: Make sure that you don't try to import the client's key into the server's host key management interface. Precision tune auto care edmond oklahoma. The host key management interface is accessed directly from the 'Server' tab of the Bitvise SSH Server Control Panel, and is intended to manage keypairs that authenticate the server. These keypairs are separate and unrelated to client authentication.
For Windows accounts, the SSH Server also supports synchronization with ~/.ssh/authorized_keys. This feature must be enabled in Advanced SSH Server settings, under Access control. It allows Windows users to upload their SSH public key to a file named authorized_keys under a subdirectory named .ssh under the user's Windows profile directory. If this setting is enabled, the SSH Server will check for the existence of the authorized_keys file when the user logs out. If the file exists, the SSH Server will replace all of the public keys configured for the user with keys found in this file.
Use this feature with caution: if your system has unused authorized_keys files laying around, this may cause public keys to be unexpectedly deleted.
There are three main ways to generate a public key in Windows. We've tried them all with Windows 7, but given the PuTTY tools are most popular, they are documented first. Whichever method you choose, email your generated key to your designated manager and they will notify you when your account has been created. Note, if you have multiple keys because you have multiple machines, or perhaps you have different keys for different software, send them all to us - we can set you up with as many keys as you want bound to your Code Enigma account.
PuTTY
This is a Free Open Source Software (FOSS) solution for Windows that allows Windows users to generate SSH keys and use them to access Linux servers via an SSH connection.
[1] Download and run the PuTTY 'Installer' from this page:
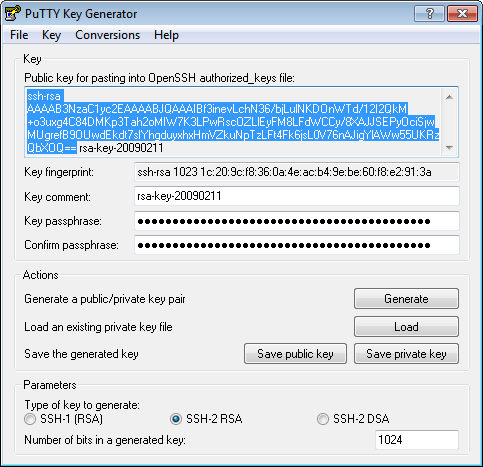
[2] Generate a private and public key pair:
- Go to the Windows Start menu -> All Programs -> PuTTY and open PuTTYgen
- Click the 'Generate' button and PuTTYgen will ask you to make some random movement with your mouse until it has enough random data to generate a secure key for you
- Click the 'Save private key' button and save the resulting file somewhere safe and only accessible by you!
[3] Export Public key to the Linux server:
In the grey box at the top, entitled 'Public key for pasting into OpenSSH authorized_keys file', there will be a string of nonsense. Copy all of this string into an email and send it to us, as per the opening instruction on this page.
That's it, you're done!
Git Bash
This is a light-weight terminal client for using Git from the command line on Windows. It's a sort of scaled down version of CygWin, and one of the nice things about it is it permits normal 'Terminal' access to Linux servers.
[1] Download and run the latest version from this page:
The installer will open msysGit when it completes, follow the instruction to create a shortcut:
[2] Generate a private and public key pair:
Follow steps 1 and 2 of the GitHub instructions found here:
At step 3, use the 'clip' command as instructed, but paste the result into an email and send it.
Bitvise
If none of the above works, there's also Bitvise, which is not FOSS, but is freely available for personal use, and even individual use within an organisation, so it's a good and legal option.
[1] Download the Bitvise SSH client software:
[2] Generate a private and public key pair: /microsoft-office-2010-professional-plus-key-generator-free.html.
Ssh Server For Windows
- click the link titled 'User keypair manager' in the Login tab;
- click the button [Generate New .];
- choose ssh-rsa and 1024bits;
- you can enter passphrase or leave it empty
- click the button [Generate]
This passphrase is not sent to the remote host, and it is only used to protect your private key. Otherwise, anyone who has access to your private key can authenticate to your account automatically.
[3] Export Public key to the Linux server:
- Go to the 'User keypair manager';
- click the keypair in the slots;
- click the button [Export];
- chose 'Export public key' and 'OpenSSH format';
- click the button [Export];
Bitvise Ftps
The result should look something like:
Bitvise Ssh Server Generate Key File
Email just this public part to Code Enigma, as per instructions.